Launching the White House Summit on Cybersecurity and Consumer Protection on Thursday, a research symposium hosted by Stanford University’s School of Engineering suggested that while the human relationship with cyberspace will continue to strengthen, educating the cybersecurity workforce and addressing consumer privacy should be the focus of our attention.
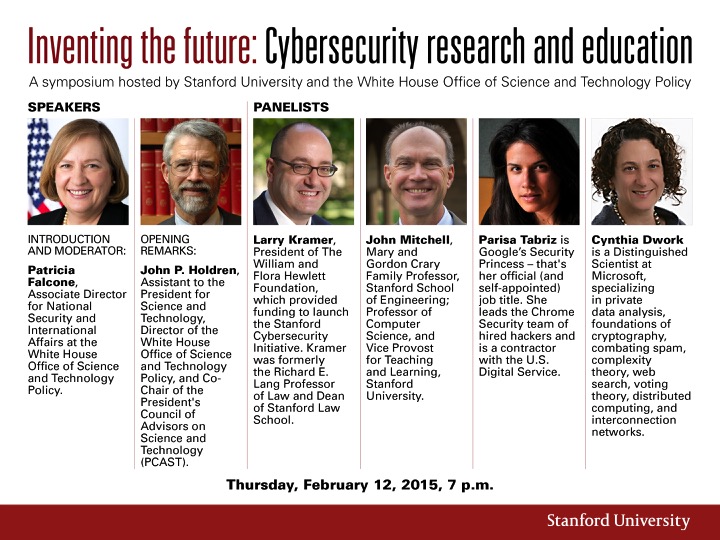
John Holdren, assistant to the President for science and technology, made clear in his opening remarks that the discussion about current issues with and the future outlook of cyberspace is important because it touches every part of daily life.
While Holdren acknowledged the innovations that have emerged from the Internet as a technological platform, he expressed concern about how public and private goods and services, for example, are also at risk through that same platform.
“Cyberspace is an asymmetric battleground,” Holdren said. “It is unfortunately easier for criminals and hackers to penetrate and disrupt our networks than it is for us to defend them.”
To address these issues, Holdren said President Obama’s administration has developed five priorities to shape the federal government’s response to this challenge. The first three, he said, are the most immediate and pressing concerns, while the fourth and fifth priorities look to the future:
- Protecting the country’s information systems and other cyber-dependent critical infrastructure from intrusions and attacks.
- Improving the ability of the government, private sector and civil society organizations to share information about cyber intrusions on a time scale that is consistent with an effective response.
- Securing federal networks by setting clear security targets and holding agencies accountable for meeting those targets.
- Engaging with international partners to build support for an open and reliable cyberspace.
- Reshaping the security landscape in cyberspace by developing a cybersecurity workforce that possesses the essential knowledge and skills.
Holdren emphasized that acquiring talented and motivated individuals to step up to the challenge of working within this field is a crucial first step.
“We are only going to find and motivate enough such individuals if we tap the nation’s entire talent pool, including women and girls and individuals from other groups historically underrepresented in STEM fields,” Holdren said.
In fact, Holdren mentioned that the demand for cybersecurity researchers and practitioners is growing 12 times faster than the job market as a whole.
Symposium panelist Larry Kramer, president of The William and Flora Hewlett Foundation, agreed that cybersecurity education is key. The Hewlett Foundation has funded research at Stanford University, MIT and Berkeley.
“We recognize it’s as important to begin to generate a talent pipeline, to create educational opportunities,” Kramer said. “And the universities are the places you have to go to do it.”
But, even if the cybersecurity workforce is larger and smarter, privacy remains a concern for the average Internet user.
Parisa Tabriz, symposium panelist and lead of Google Chrome’s security team of hired hackers, said the issue of privacy is a personal one. This specificity may make it difficult to ensure satisfaction of one type of privacy for every individual.
“I want to emphasize the human component to this problem,” Tabriz said. “Privacy is so personal and so specific to culture and your specific situation.”
Panelist Cynthia Dwork, a distinguished scientist at Microsoft specializing in private data analysis, suggested that perhaps privacy is being thought of in the wrong way. Dwork said people should “question every assumption” and that although there is concern about being treated unfairly, privacy is not necessarily the solution concept to ensure fairness.
Panelist John Mitchell — professor of computer science and vice provost for teaching and learning at Stanford University — frequently deals with the cross-section of cyberspace education and concerns of cyberspace privacy.
Mitchell said Stanford has been involved in expanding educational opportunities by combining online learning activities for individuals via free public courses, from which data can be collected regarding the learning patterns of individuals.
But, it’s “a balancing act.” There is tension between making data available and protecting the privacy of individuals.
“As technology evolves and new ways of collected data evolves, we need a social process around that so that as users of systems can become comfortable with the data collection,” Mitchell said, “and also we can begin to articulate the kind of boundaries that we don’t want to cross and ways that the data could be used.”
